The National Cyber Security Centre (NCSC) 10 Steps to Cyber Security has become a best practice cyber benchmark in the UK. This post describes a logical approach to implement their guidance as part of your Information Security Management System (ISMS).
Pratical Ways to Implement the NCSC 10 Steps into your ISMS
The NCSC 10 Steps provides a broad set of capabilities to measure an existing ISMS or to provide the foundation to build a new one. The NCSC 10 Steps provides a useful benchmark to identify good work, weaknesses and improvements across people, process and technology. Your ability to demonstrate compliance will boost stakeholder, public and partner confidence in your cyber security readiness.
In this blog, we will look at key findings and practical ways to implement the steps supported by a comprehensive guide that you can download here.

The NCSC 10 Steps rely on an ISMS
“Step 1” and the heart of the NCSC approach requires us to “set up your risk management regime”. This is an ISMS by another name, whether you are seeking compliance with ISO27001, or adopting a less stringent but still structured approach.
An ISMS requires you to perform asset identification, risk management and the application of controls to address vulnerabilities. To understand the breadth of the task, this link takes you to our post on ISMS Design, Build and Maintenance.
To recap, the benefits of an ISMS include:
1. Information asset understanding and Data Protection
2. New ways to make operational use of assets – it isn’t just about security!
3. Improved identification of security gaps and vulnerabilities
4. Visibility of the evolving information risk profile.

However, without the first step of an ISMS or “risk management regime“, as the NCSC describe it, you lack the strategy that glues different controls and processes together. This will lead to fragmented cyber security, hidden vulnerabilities and potential for compromise. This also leads to an inability to measure the risk profile.
NCSC 10 Steps: A Tiered Implementation
Our implementation plan for the NCSC 10 steps, divides them into 4 groups. The groups can be distinguished by their role, sophistication and complexity. The 4th “deliver” group identifies 2 steps as parallel activities.

This approach is similar to how we might group together assets in the ISMS that receive similar risk treatment. Grouping of the NCSC steps helps stakeholders better understand the implementation and maintenance effort required.
Group 1 – NCSC Steps to “Establish” Cyber Security
Secure configuration, monitoring and incident management are the least complex activities that should be in place. Undoubtedly some might perceive these 3 activities as time consuming, but this does not make them difficult.
Taking secure configuration as the example (the supporting document gives more detail), most organisations will in theory be using supported software. They will also routinely deploy patches, have baseline IT builds and will prevent users changing security settings.

Bringing implementation of Group 1 into sharp focus are the pressures of EUGDPR that require data protection and security. Organisations that don’t bother with a secure IT baseline, are not able to monitor for breaches and cannot respond to incidents when they occur, are risking severe financial penalties.
Group 2 – NCSC Steps to “Manage” the ISMS
In this group, we suggest that managing user privileges and network security are complex to meaningfully achieve.
When managing user privileges, the complexity comes from the fact that you have to understand the access required by your users and the operational roles they undertake before you can apply control. This will require a degree of cooperation between business stakeholders, the IT and security teams to establish an approach.

The challenge is often further complicated where any existing or legacy systems have no clear access requirements defined or enforced. Even when you start afresh (e.g. a new app), often the business or users have little understanding of the access requirements.
In the case of network security, complexity can be introduced by the adoption of cloud and the concept of “de-perimeterisation”. This is the challenge of knowing where the network begins and ends before you can consider how to secure it. The likelihood for most is a hybrid approach of an on-premise IT estate (that you secure), with applications, storage capacity and data migrating to cloud (that the provider secures).
Group 3 – “Enhanced” NCSC steps for Protection
This group includes the NCSC guidance on malware prevention and removable media control. Some readers may not consider either to be particularly complex especially for those in established and ISMS driven security environments.
What crystallized the issue was the impact of attacks such as Wannacry. High profile attacks such as this, publicly demonstrated that organisations with a wealth of sensitive data that should have effective cyber security controls, may still be struggling.

The complexity of dealing with malware increases when the variety of ways it can be introduced to the network are considered. Our Quad9 post listed some of these ways but in summary, user education should be considered as a prevention option just as much as an anti-malware server. Any one measure in isolation is unlikely to be sufficient and a combination of approaches needs to be adopted.
The “Parallel” NCSC steps in your ISMS
There are 2 NCSC steps that should be delivered in parallel to the others: User education and awareness and home and mobile working.
User education and awareness is a never-ending ISMS task complicated by “movers, leavers and joiners”. The only real solution is a continuous and managed approach that involves, HR, the training department, managers and the employees themselves.

Similarly, mobile and home working require cross department consideration as to:
- Who requires access and their priority for it?
- How access will be facilitated and protected?
- When is access required? (e.g. out of hours, annual leave periods etc.)
- Where will access be granted? (e.g. is out of country access to be denied?)
- Why mobile working will enable and support business?
These questions are particularly challenging for the public sector. Where permitted, you will first need security policy that is backed up with subsequent enforcement by way of continual monitoring and device control.
Given the effort required to guide, train and protect users, continual and parallel engagement across user and delivery teams is vital.
ISMS Challenge: Balancing Business with Security
As with all cyber security approaches, be it the NCSC approach or measures you adopt from elsewhere, delivering and monitoring cyber security effectively whilst avoiding unnecessary burdens for users will be both an objective and challenge for your ISMS.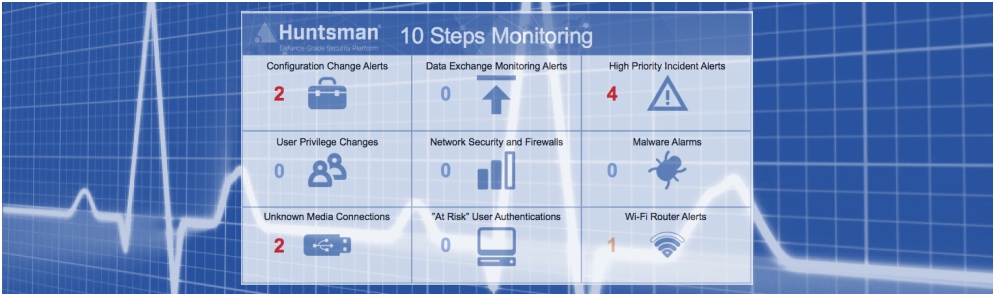
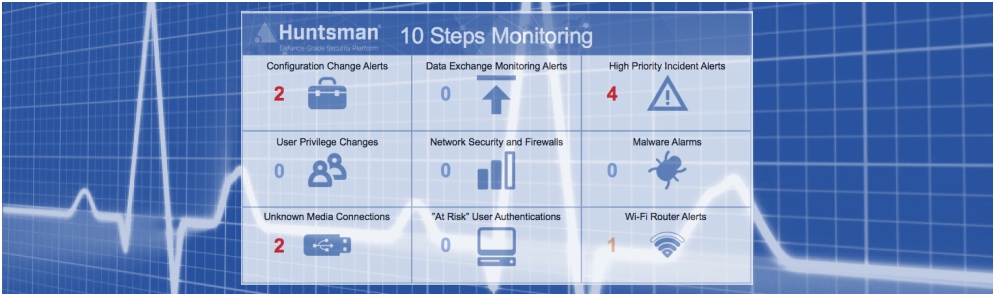
Just as an ISMS requires the review of vulnerabilities and controls used to mitigate them, the monitoring of NCSC 10 Steps compliance can help drive success.
The sooner you identify and address any causes for concern in the way systems and data are protected, the safer your organisation will be and the greater the chance of reducing loss.
 About Huntsman
About Huntsman