Outcome-Driven Metrics and Protection Level Agreements
We serve some of the most sensitive and secure intelligence, defence and criminal justice environments in the world.
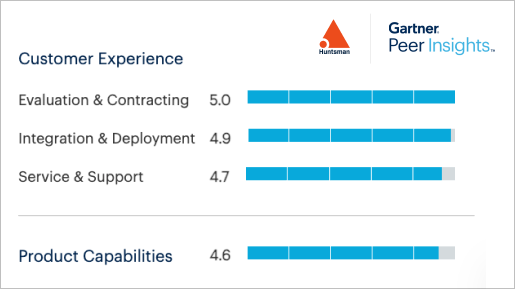
Our platform is purpose-built for security-conscious organisations with complex requirements. Discover how Huntsman Security compares to other SIEM solutions, with outstanding review scores for deployment, support, and product quality.

with cost-effective, automated applications with significant demonstrable ROI
cyber maturity and cyber gap reporting in minutes, that protects IT assets, systems and sensitive information on-site and in remote locations
with data-driven reporting for tech teams and executives to visually see and benchmark your cyber risk status, supported by in-built prompts to remediate issues
Automate your data collection and audit functions with the Essential 8 Auditor.
It turns complex security data into actionable reporting for risk management decision-making, providing a faster and more accurate assessment of your cyber posture.
Find out more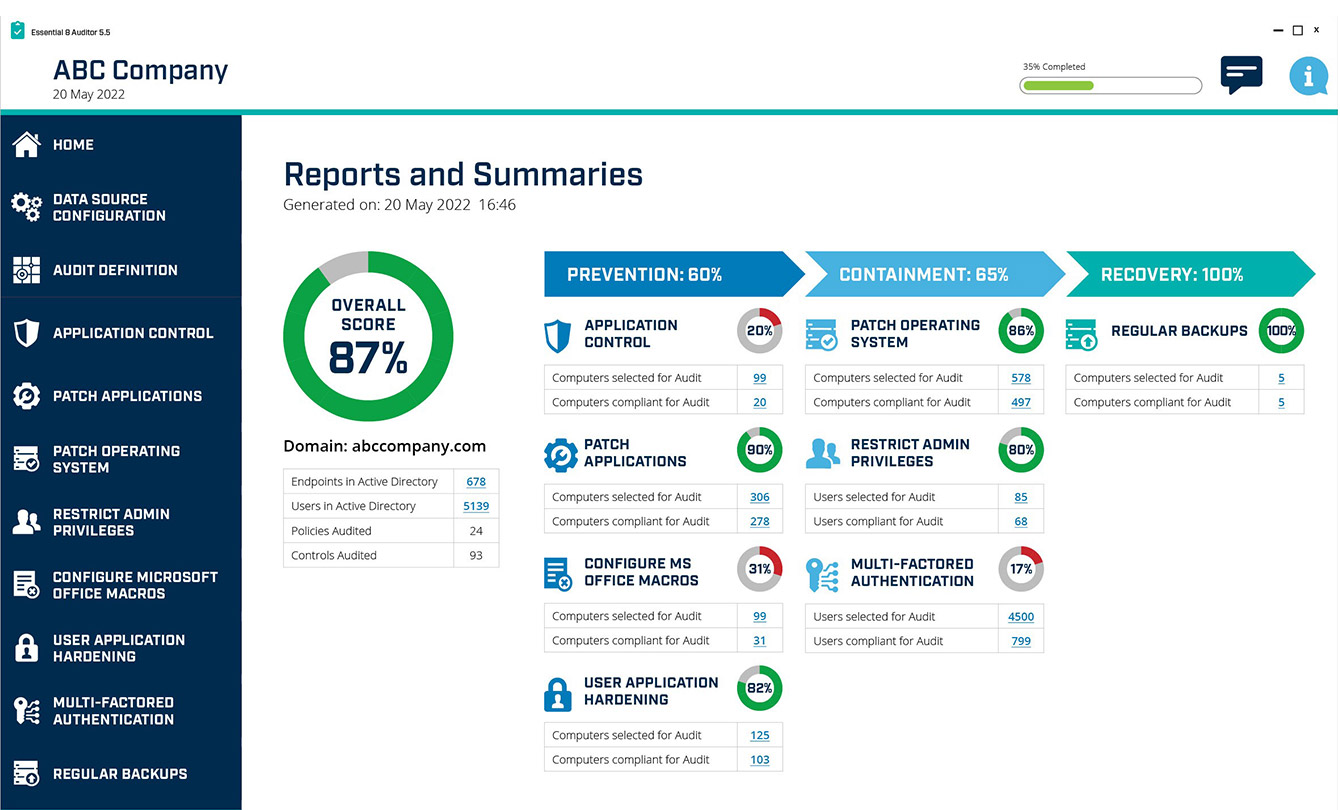
Read by directors, executives, and security professionals globally, operating in the most complex of security environments.