Outcome-Driven Metrics and Protection Level Agreements
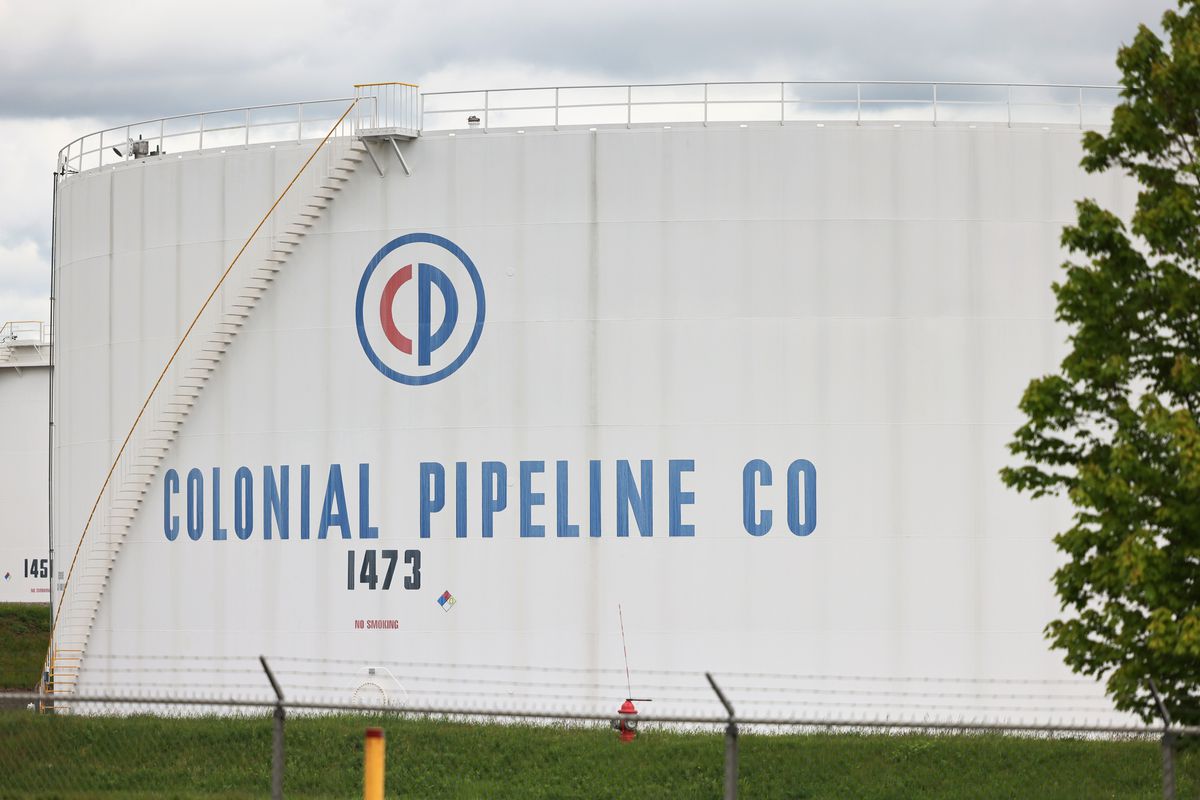
Ransomware is a clear and present danger to business and if any organisation needs convincing, events impacting Colonial Pipeline Co this week are a clear reminder. Critical Infrastructure (CI) operators everywhere have been warned by authorities of their potential vulnerability to cyber attack; efforts are being made in some industries but the overall shift towards resilience across the sector remains slow.
The execution of ransomware attacks is, by now, almost an industrialised process. Its delivery is customised, professional and troublingly effective. Recent statements by those responsible for this latest Colonial Pipeline CI attack, reveal a touch of PR irony with their apparently socially responsible efforts to go after data for money, rather than to cause problems for society.
Ransomware continues to be a threat for all businesses, and of even greater concern for a society that relies on CI businesses that provide their every financial, communications, transportation and utility needs.
Frustratingly this will not be the last report of unplanned events that have led to disruption to one of the many and varied CI services that underpin much of our daily lives. For the company’s IT security team and Colonial Pipeline more generally, the weekend of May 8th and 9th went downhill pretty quickly.
Colonial Pipeline Co runs an oil distribution pipeline up and down the US east coast. For the US, with its heavy reliance on the automobile, this is about as close to mission critical as you can get. Any disruption was bound to lead to community concerns.
Colonial was hit by a ransomware attack. Initial signs were that the effects were contained and that only 100Gb of data was affected (although who knows at this stage what that data was). Nevertheless, the pipeline control systems and so the pipeline itself were shut down.
Whether the loss of the pipeline service was a result of the attack or a controlled response by the security team, the outcome has impacted the community way beyond the business itself. It is for this reason that in the eyes of many regulators, CI providers now carry broader social responsibilities to protect their businesses from cyber attacks and their communities that depend so much on them.
We have seen several times now the effects of a ransomware attack on IT systems spilling over into the real world. There were cancelled operations and appointments when WannaCry hit the NHS in the UK, and lost and inaccessible foreign currency orders and transactions resulting from the Travelex case.
In this most recent Colonial Pipeline attack, the inability to pipe fuel meant the Declaration of a State of Emergency in several states following major concerns about how such massive volumes of oil could be safely moved and predictions of significant pump price rises for consumers. One can only contemplate the much broader implications if it was financial services, water or electricity that was disrupted.
Many governments are already moving to tighten up cyber security requirements for CI organisations, particularly those that are key to the normal functioning of society.
In the US this has been accelerated by recent events, in the UK and across Europe where the EU NIS directive is being reviewed and controls reconsidered.
In Australia, there are also changes happening in relation to categorisation of CI industries, with cyber security coming under greater focus from regulators, particularly priority industries, with the emergence of the concept of “positive security obligations”. There are also wider initiatives in corporate and IT governance around the duties and resulting risk management responsibilities for directors and officers.
At a more direct level:
This containment of a threat in reaction to a malware incident can have implications for the business but also its broader stakeholders. Does it mean fuel shortages, a need for additional ground transportation as a contingency, the interruption to vital utilities or a closed hospital?
Critical Infrastructure is designated “critical” for a reason. The uninterrupted operation of many of these services is vital for the ongoing operation of our society and wellbeing. Many CI players are yet to satisfactorily renovate their IT and IoT systems and the introduction of ransomware results in a potentially incendiary mix.
The Colonial Pipeline Co experience could have been so much worse and it should act as a reminder for all of us. Implement a cyber improvement program that regularly measures your IT security performance against a recognised IT risk framework. Focus on improving the maturity of your cyber security controls and form a risk management perspective plan for the almost inevitability that you too will come under cyber attack.
Read the details of the Colonial story at the links below, but this situation is still unfolding, so we will all have to see how it develops:
https://www.bbc.co.uk/news/business-57050690
https://www.huffpost.com/entry/cyberattack-colonial-pipeline_n_60969a73e4b05bee44caa2bf
https://www.washingtonpost.com/business/2021/05/08/cyber-attack-colonial-pipeline/
Read by directors, executives, and security professionals globally, operating in the most complex of security environments.