Outcome-Driven Metrics and Protection Level Agreements
Huntsman Security’s Essential Eight solutions accurately measure security control effectiveness and maturity levels against the ACSC Essential Eight Maturity Model; to improve compliance, provide visibility and enable informed oversight for risk management and compliance.

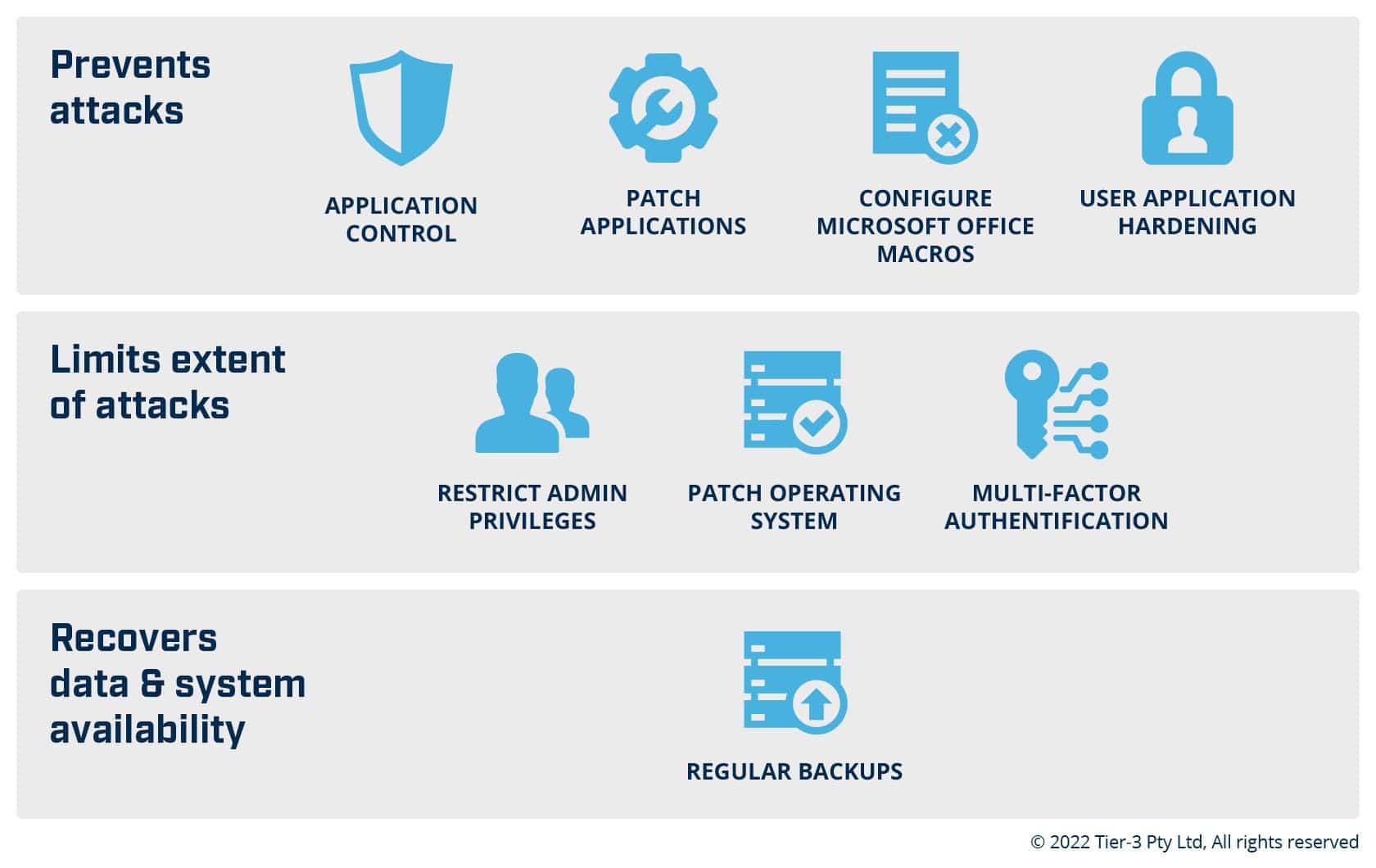
The Australian Cyber Security Centre’s ACSC Essential Eight risk management framework is a prioritised list of eight mitigation strategies (security controls) organisations can implement to protect their systems against a range of adversaries. The ACSC recommends the implementation of the eight controls as a baseline, to help mitigate the majority of cyber threats.
On 15 March 2022, the Attorney-General’s Department’s Protective Security Policy Framework (PSPF) was updated to mandate the Essential Eight, Maturity Level Two for all non-corporate Commonwealth entities.
Australian State and Territory governments require their agencies to report on compliance with a mandated information security policy. In NSW, QLD and WA, the information security policies mandate compliance with the ACSC Essential Eight with annual reporting required.
The ACSC recommends that all organisations implement the Essential Eight security controls as they are the most effective mitigation strategies to help organisations protect themselves against various cyber threats.
Whether your operation sits within federal or state government, or is a private enterprise, you will require monitoring, measurement and reporting to assess your current status and ongoing compliance posture against the Essential Eight risk mitigation strategies.
Huntsman Security’s Essential Eight measurement, compliance and reporting solutions, Essential 8 Auditor and Essential 8 Scorecard, collect and analyse events from your infrastructure, systems, services and applications to produce your maturity score against the ACSC Essential Eight, and give all parties a clear picture of your cyber security control effectiveness.
The Essential 8 Auditor provides on-demand cyber vulnerability and maturity assessment, to measure your security compliance against the ACSC Essential Eight framework. It allows you to measure your Essential Eight maturity score in minutes, and then produces a comprehensive ‘to-do’ list of issues for resolution for your Security & Risk team.
The Essential 8 Scorecard provides continuous cyber risk measurement by monitoring and reporting on your organisation’s ongoing security control effectiveness against the ACSC Essential Eight, either directly or via your IRM platform.
Download our Essential Eight Compliance Guide to discover how to measure the effectiveness of your organisation’s security controls using Huntsman Security’s Essential Eight solutions.
Read by directors, executives, and security professionals globally, operating in the most complex of security environments.