Outcome-Driven Metrics and Protection Level Agreements
The GDPR is a regulatory framework for data protection and privacy. It came into effect in the EU, including the UK, on 25 May 2018 and was subsequently incorporated into UK law post-Brexit to create a substantially similar UK version. GDPR contains 99 Articles covering virtually every aspect of business and information management – from the consent to collect and process information, to the “right to be forgotten”. Importantly for global businesses (including those outside the EU and UK) the GDPR is supra-national, therefore any business that processes the data of EU or UK citizens will fall under its remit.
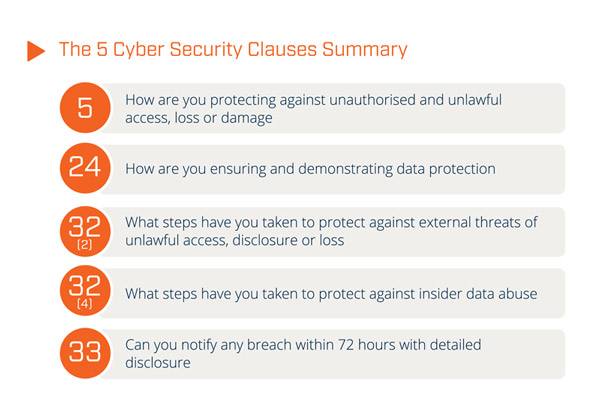
For cyber security professionals, the drive for data protection and information management is not new; although the level of detail, the requirements on data breach notification and the fines in GDPR impose a lot more focus. There are five individual articles that have specific cyber security implications:
For security monitoring and operations in GDPR compliant businesses there is increased focus on both prevention and avoidance of security and privacy breaches. Further, it is imperative to be able to respond quickly when a problem does occur, understand it and take action. The 72 hours allowed to notify the regulator is accompanied by an expectation that affected data subjects will, in certain cases, be communicated with promptly. As a minimum, businesses handling personal data will need to:
Knowing where to start with the implementation of the 5 cyber security articles of GDPR is key to success. Would you like to find out how? Our Fast Track GDPR Guide will help you:
Enterprise SIEM
Huntsman Security’s Enterprise SIEM software provides flexibility, visibility and effective use of resources in security monitoring, information protection and breach response to deliver the following:
Essential 8 Scorecard
The Essential 8 Scorecard provides continuous measurement of key security controls to prevent, limit and recover from breaches by:


Read by directors, executives, and security professionals globally, operating in the most complex of security environments.