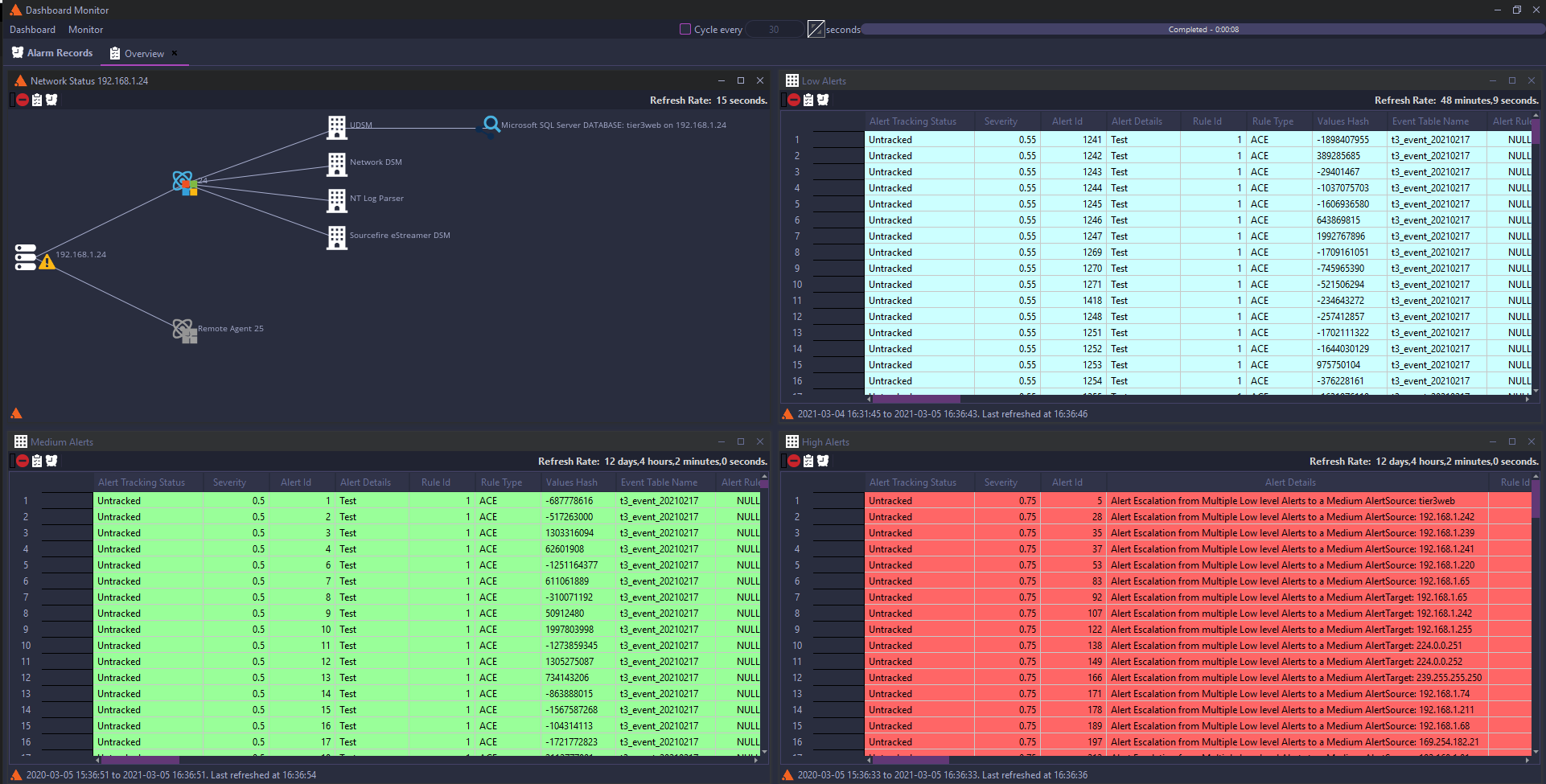
For internal SOCs (scale & flexibility)
- Defence-grade analytics and Live MITRE ATT&CK® heatmaps for threat context and prioritisation.
- Flexible on-prem/virtual / cloud deployment and hierarchical data storage for long-term retention and federated enterprises.
- High performance in-stream processing ( >150k EPS on standard platforms).
Best suited for internal SOCs that need high throughput, on-board incident management, easy compliance reporting and an analyst-friendly interface.
Download Brochure →