Outcome-Driven Metrics and Protection Level Agreements

This week saw the announcement that British Airways (BA) was to be fined by the Information Commissioner for its breach of the GDPR. The proposed fine amounts to £183m so it caught the attention of the security and legal/compliance community as being the first really notable GDPR case with a big fine attached.
There was no shortage of news coverage (including with comment from Huntsman Security) such as:
And the BBC of course at:
The breach, dating back to June 2018, involved the web site – traffic to which was diverted to a fraudsters page so that user information and payment details (including CVV codes) could be harvested. 500,000 people are understood to have been affected.
In the ICO’s statement they noted that “poor security arrangements” compromised a variety of information at the company. This highlights two challenges that all business face:
These twin imperatives should be seen in parallel. If you don’t know what state your basic cyber hygiene controls are in its difficult to justify the time/effort/investment to improve them. Hence, being able to measure/audit/report on things like patching, control of admin privileges and browser security is key to not only know where effort is needed, but also to be able to provide confidence and visibility.
No one in the senior management team of any company wants their business to be in a position where a £183m fine is a possibility. Yet, without clear reporting on the effective delivery of the security process and the trustworthiness of the environment, there is a huge gap in the understanding of the risks that the business faces.
The other reason for getting basic cyber security controls in place and then monitoring them thereafter is that effort can then move to more insidious threats and more complex defences. The MITRE ATT&CK framework is a few levels further on for most organisations. The range of attack techniques and impacts is quite daunting! But there’s little point considering that as a model for delivering security if you are still running unpatched operating systems or – worse – if you don’t know what state your operating system patching is in.
After all you wouldn’t fly a plane if you didn’t have a reliable altimeter to tell you whether you were in danger of crashing, and you wouldn’t run an airline without knowing where your planes were and what passengers and flightpaths you had to deal with.
The BA case is undoubtedly a large fine, even if it ends up being reduced in later negotiations, it has still served its purpose – highlighting the direct consequences that businesses face in the era of GDPR.
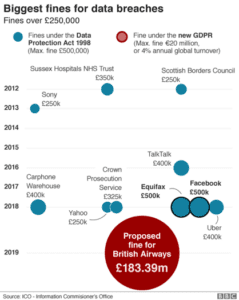
GDPR fines will be bigger
Without the right technology and processes in place, and most importantly without the understanding of whether they are doing enough to reduce risk, organisations could swiftly find themselves in the firing line for similarly painful sanctions, not to mention the potential damage to their reputation and loss of custom.
To better deal with this issue, cyber security must become a boardroom level issue – where every part of the business has real visibility and a clear understanding of current residual risk.
This needs to extend not only across the business, but to anyone it works with that could potentially jeopardise data security. Businesses that don’t follow this could swiftly find themselves as the next example for the industry.
Read by directors, executives, and security professionals globally, operating in the most complex of security environments.